You need to prepopulate the password for User1 on DC2. What should you do first?
RODC
As about of you were enlightened, I published my volume "Mastering Active Directory" back in, 2017. When I released information technology, I had my doubts! It was my first book even though I was writing to blogs for many years. But over the last 2 years, I had many positive feedbacks. Thousands of people all effectually the global read this volume. Lots of them requested another book. So Yes! I heard information technology loud and clear.
I glad to announce the public release of my second book, "Mastering Agile Directory, Second Edition" today. It is bachelor for purchase worldwide at present.
I too take this opportunity to thanks all my readers who believed in me. It is you who encouraged me to release some other edition this soon.
What Is new in the 2d edition?
The new content for this edition is roofing,
• Tips to Design your Hybrid Advertizing environment by evaluating business and technology requirements
• Deep dive into different hallmark methods which tin can use in Hybrid AD surround
• How to protect sensitive data in a hybrid surround using Azure Information Protection
• Learn nearly protecting identities in Hybrid AD surroundings
• Integrate with Azure Active Directory and Manage identities in Hybrid Environment using Azure Active Directory PowerShell for Graph module
Book Name: Mastering Active Directory, Second Edition
ISBN: 978-1789800203
Number of Pages: 786
Publisher: Packt Publishing
Book is available in paperback and kindle format.
It too can access via subscriptions,
https://www.packtpub.com/cloud-networking/mastering-active-directory-2nd-edition
RODC are a bully feature which is introduce with windows server 2008 in order to maintain a low gamble domain controller in locations where information technology cannot guarantee physical security and the maintenance. Though out commodity nosotros have discussed possible scenarios where we required a domain controller in a remote site. When because a domain controller in remote site, the link betwixt site is not the only thing we need to focus on. When nosotros deploy a domain controller, by default it volition exist enlightened of any changes in agile directory structure. Once an update trigger, it updates its own re-create of the active directory database. This ntds.dit file is contain everything nearly active directory infrastructure, including identity data of the user objects. If its falls in to wrong hands, they can call up data related to identities and compromise the identity infrastructure. when consider near information security, the physical security is as well of import. That's why the datacenters accept al sort of security standards. And so, when deploying a domain controller in remote site, physical security likewise a consideration as we do not demand to accept loose ends. If you lot have a requirement for domain controller in remote site and withal yous cannot confirm its security the RODC is the answer. RODC practice not shop any password in its database. All the authentication request against an object volition exist process by the closest writable domain controller. Then even someone manage to get copy of the database they will non be able to practise much.
RODC deployment process involves following stages. In this process, we can use a pre-selected account and promote the RODC using it instead of using Domain Admin or Enterprise Administrator account.
1) Setup Computer Business relationship for RODC domain controller
2) Attached that account to the RODC during the promo process
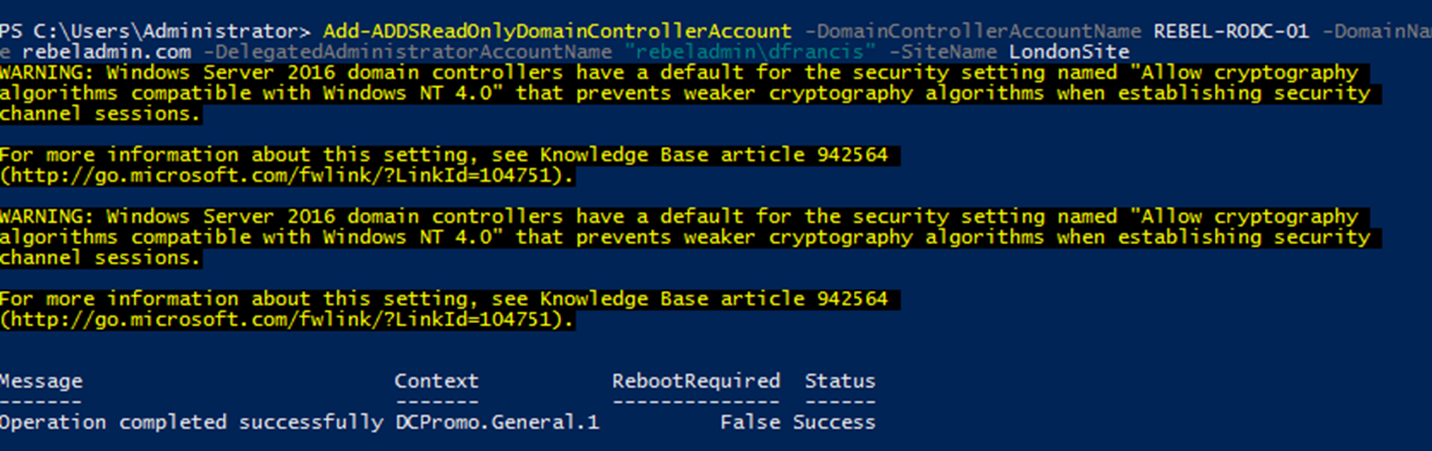
In order to create RODC estimator account we tin can apply Add-ADDSReadOnlyDomainControllerAccount cmdlet.
Add-ADDSReadOnlyDomainControllerAccount -DomainControllerAccountName REBEL-RODC-01 -DomainName rebeladmin.com -DelegatedAdministratorAccountName "rebeladmin\dfrancis" -SiteName LondonSite
Above command will create RODC domain controller account for Insubordinate-RODC-01. The domain name is defined using -DomainName and -DelegatedAdministratorAccountName defines which account to delegate the RODC installation. The new RODC will exist identify in LondonSite.
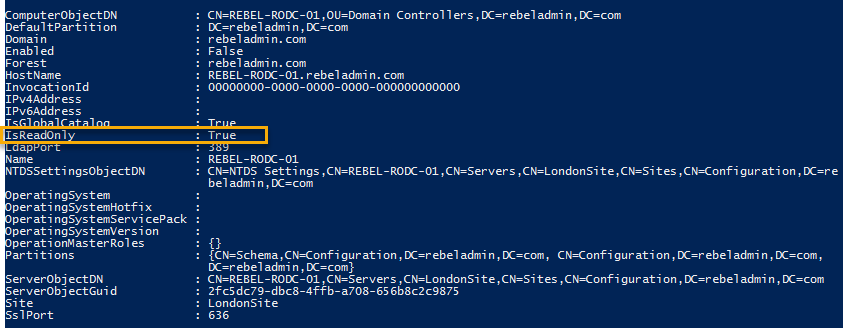
Now we tin can see the newly added object under the Active Directory Domain Controllers.
Now nosotros have things ready for the new RODC and adjacent step is to promote information technology.
Install-WindowsFeature –Name AD-Domain-Services -IncludeManagementTools
Higher up control will install the Ad DS office first in the RODC. Once its completed nosotros tin promote it using,
Import-Module ADDSDeployment
Install-ADDSDomainController `
-Credential (Get-Credential) `
-CriticalReplicationOnly:$false `
-DatabasePath "C:\Windows\NTDS" `
-DomainName "rebeladmin.com" `
-LogPath "C:\Windows\NTDS" `
-ReplicationSourceDC "Insubordinate-PDC-01.rebeladmin.com" `
-SYSVOLPath "C:\Windows\SYSVOL" `
-UseExistingAccount:$true `
-Norebootoncompletion:$false
-Forcefulness:$true
In one case this is executed it will prompt for the user account and we need to input user account info which was delegated for RODC deployment. The command is very like to regular domain promotion.
Now we have the RODC and adjacent steps to look in to password replication policies (PRPs).
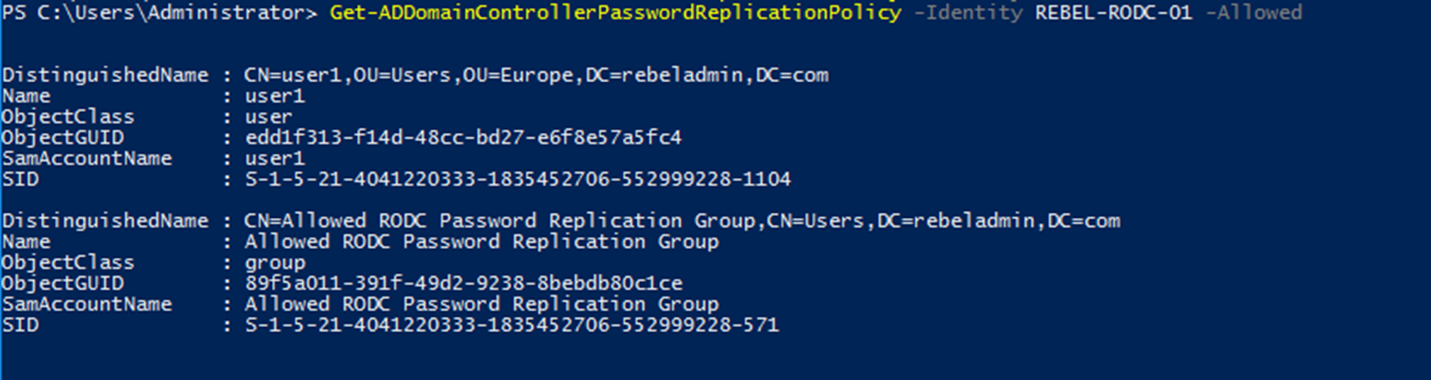
The default policy is already in place and we tin view the allowed and denied list using,
Go-ADDomainControllerPasswordReplicationPolicy -Identity Insubordinate-RODC-01 -Allowed
Above control volition listing down the immune objects for password caching. By default, a security group chosen "Immune RODC Password Replication Group" is allowed for the replication. This doesn't contain whatsoever members past default. By adding object to this grouping will allow caching.
Become-ADDomainControllerPasswordReplicationPolicy -Identity Rebel-RODC-01 -Denied
Above command list down the denied objects for countersign caching. By default, post-obit security groups are in the denied list.
• Denied RODC Password Replication Grouping
• Account Operators
• Server Operators
• Backup Operators
• Administrators
These are loftier privileged accounts in active directory infrastructure these should not be cached at all. By adding objects to Denied RODC Password Replication Grouping, we tin can merely block the replication.
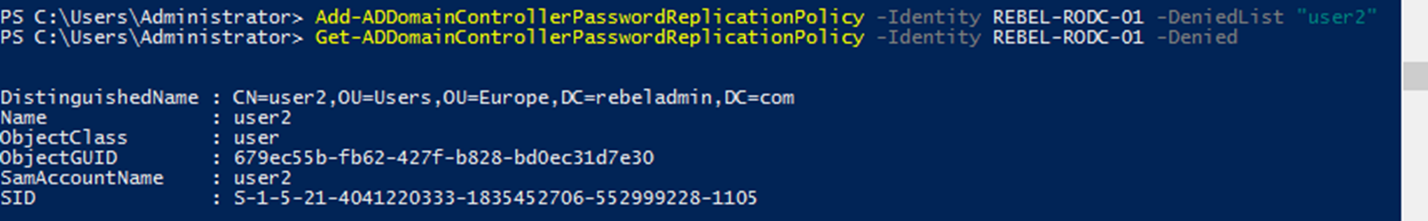
Autonomously from the utilise of predefine security groups we tin can add objects to allow and denied list using Add-ADDomainControllerPasswordReplicationPolicy cmdlet.
Add-ADDomainControllerPasswordReplicationPolicy -Identity REBEL-RODC-01 -AllowedList "user1"
Above command will add user object user1 to the immune list.
Add-ADDomainControllerPasswordReplicationPolicy -Identity REBEL-RODC-01 -DeniedList "user2"
The above command volition add the user object "user2" to the denied list.
This marks the end of this blog post. If you lot have whatsoever questions feel free to contact me on rebeladm@alive.com also follow me on twitter @rebeladm to get updates almost new weblog posts.
In last 2 posts I accept explain benifits of the RODC and how we can deploy a RODC. if y'all haven't read them however you can read them with following links,
Why Read-only domain controllers (RODC) ?
Step-past-Pace guide to install Read-Merely Domain Controller (RODC)
In RODC environment one of the great feature is the countersign replication. in RODC environment we can determine which passwords need to be cache in RODC and which accounts still need to be cosign via writable domain controller. Equally example domain administrator accounts do not need to be cached on RODC. its always safe if it can exist authaticate via routable DC for security purposes. so if a domain administrator login from a RODC enviornment, we can set organisation to forward the authtication request or service ticket to the writable domain controller.
Microsoft made this easy by introducing password replication policy (PRP) to RODC environment. by default system create domain-wide password replication policy two domain local security groups.
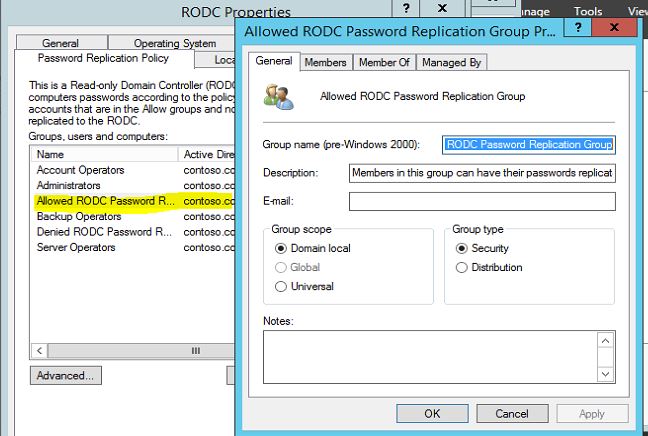
Allowed RODC Password Replication Grouping : Members of this group will permit to cache passwords in RODC. by default this group do not have whatever members.
Denied RODC Password Replication Group: Members of this group are deny to cache passwords in RODC. Some of the groups which are security critical are member of this group past default such as Administrators, Server Operators, Backup Operators, Account Operators.
1 of the biggest mistakes administrator do is only allow/deny user accounts. Just computers it cocky too uses authatication and service tickets requests. and so make sure y'all add computer accounts also in to these lists.
How to configure RODC countersign replication policy(PRP) ?
1) Login to a writable domain controller with domain ambassador account
ii) Open "Active Directory Users and Computers" snap in past Server Manager > Tools > Active Directory Users and Computers
3) Go to "Domain Controllers" OU
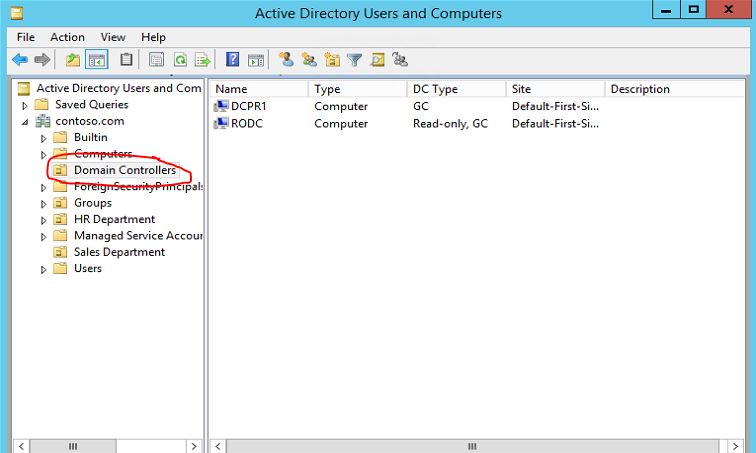
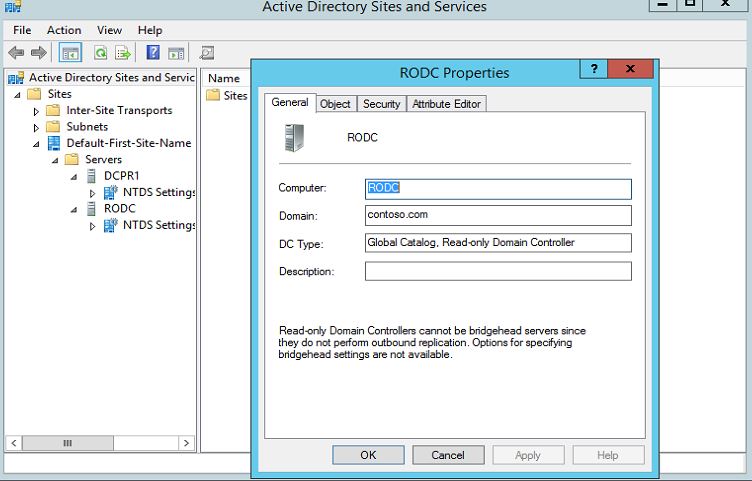
iv) Click to select the RODC y'all demand to configure PRP. And so right click and click on properties.
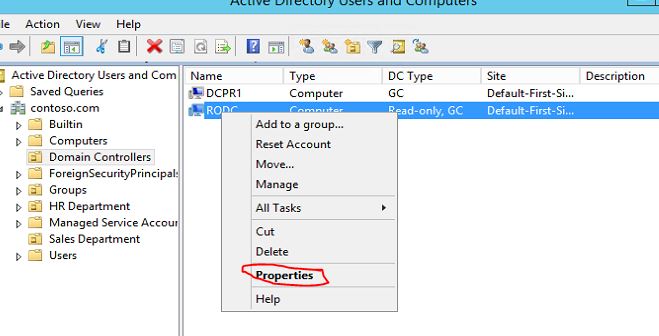
v) In the backdrop window click on "Countersign Replication Policy" tab
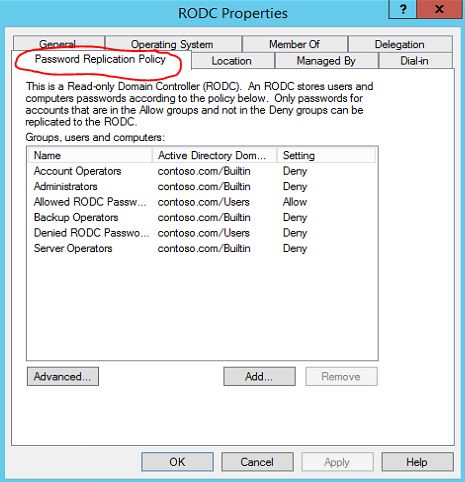
six) In there we can see the 2 groups i mentioned above.

7) Nosotros can add users to these groups. to add users/computers to those double click on the group. in here i volition use "Allowed RODC Password Replication Group"
8) To add together users/computers to grouping click on members tab and click on add.
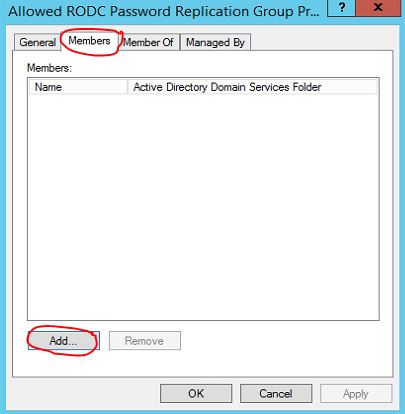
9) Once users/computers added click on "OK" to apply changes.
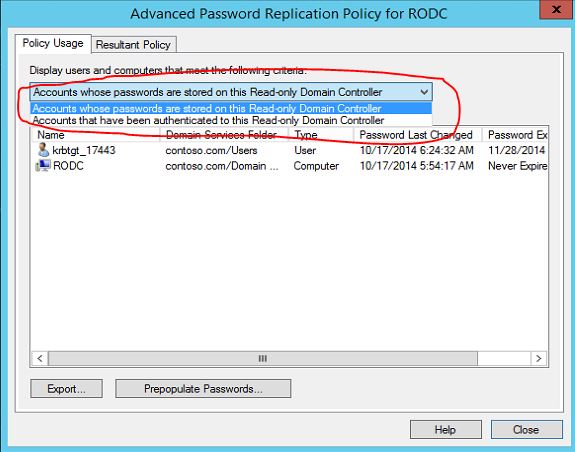
Policy Usage Reports and Pre-Populate Credential Caching
Microsoft provided a easy method of reporting where we can check the status of password replication. in order to apply this facility need to follow following steps.
one) Login to a writable domain controller with domain administrator account
2) Open "Agile Directory Users and Computers" snap in by Server Director > Tools > Active Directory Users and Computers
3) Go to "Domain Controllers" OU
4) Click to select the RODC yous need to configure PRP. Then right click and click on properties.
v) In the properties window click on "Password Replication Policy" tab
half dozen) Click on "Advanced" button
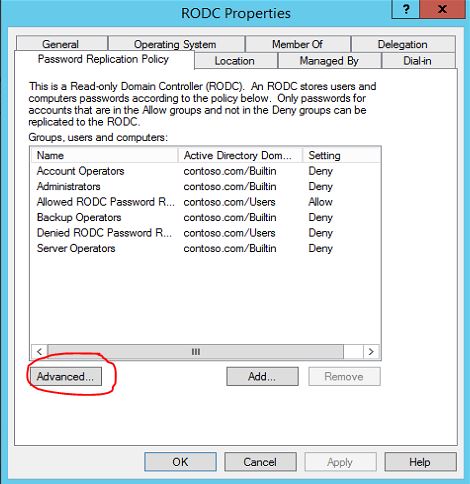
7) In here drop-down list in that location is 2 options listed
Accounts Whose Passwords Are Stored On This Read-Only Domain Controller: This choice will list all the user accounts/computer accounts which are currently cached password on RODC.
Accounts That Have Been Authenticated To This Read-Just Domain Controller: This option volition list the user accounts/reckoner accounts which were forwarded to writable domain controller for authentication and service tickets process. This is good place to identify the user accounts/ calculator accounts which will nonetheless need to add to allow list for password caching.
In PRP lets assume nosotros allowed USER A to cache his credentials in RODC. But it will non enshroud it right away. information technology will cache credential one time user fabricated first authentication request to the RODC. but microsoft given opertunity where nosotros tin pre-populate the caching. so when user login first fourth dimension his password is already been buried on RODC.
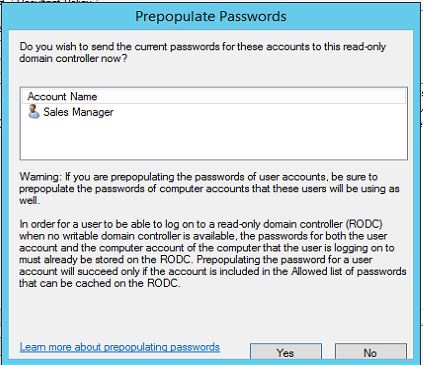
In order to employ this feature click on "Pre-Populate Passwords…" button in same accelerate window.
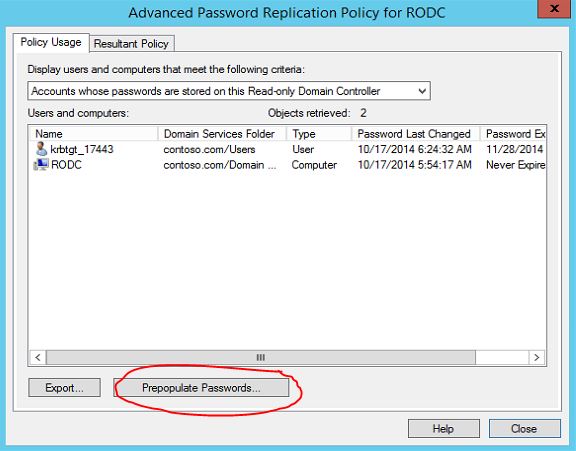
It will open up up window where you can select the accounts you need. once its selected it volition pop-up following information window. click on yes to accept the changes.
before do this make sure you have already allow that user/computer account in Allow list of password caching.
if you lot accept any questions delight feel complimentary to contact me on rebeladm@live.com
In previous mail service i take explain what is RODC and the benefits of it. If you not read it yet you can find it in here.
Before install a RODC in a domain environment it need to meet the following requirements,
- Forest function level should be windows 2003 server or higher
- Needs at to the lowest degree one writable domain controller running windows server 2008 or higher
If forest take any DC running windows server 2003 we demand to adjust permissions on DNS application directory sectionalization to allow them to replicate to RODC. It can exist done by running adprep /RODCprep from windows 2012 server installation disk \back up\adprep folder.
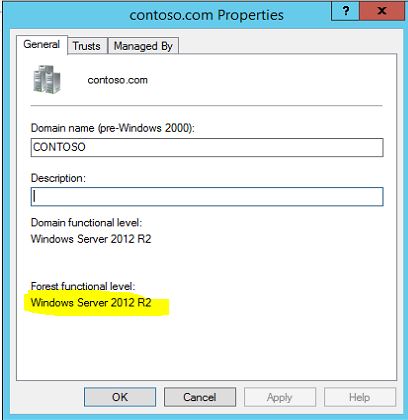
In my demo setup i exercise have a domain called contoso. Before start lets bank check the forest function level.
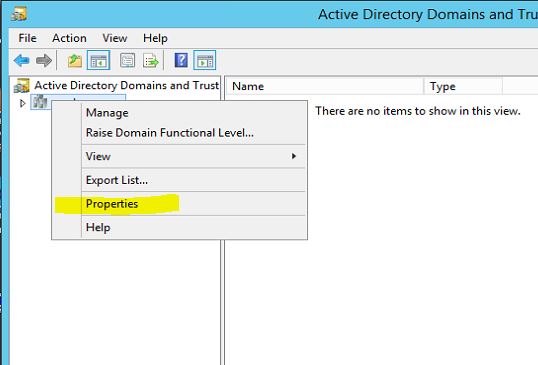
- To do that, log in to the DC every bit domain admin and open "Server Manager"
- Then from tools click on "Active Directory Domains and Trust"
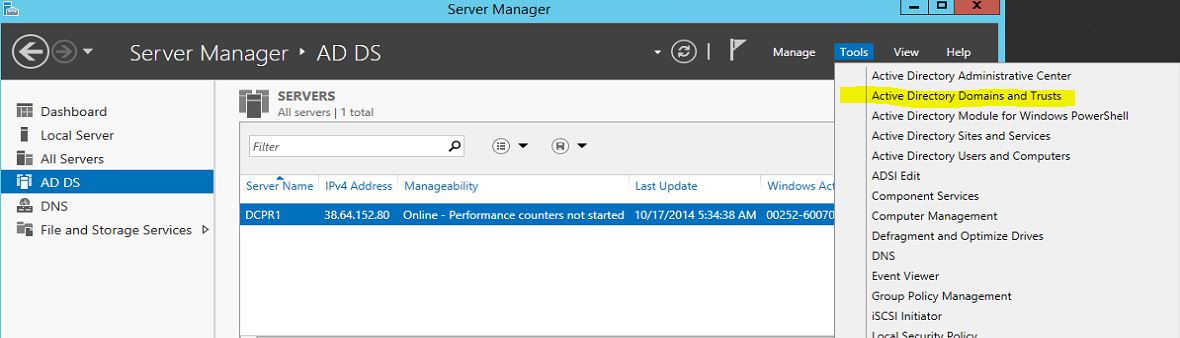
- Right click on domain and select "Properties"
As we tin see here its runs with windows server 2012 R2 so we do not need to prepare domain with adprep /RODCprep
To install RODC i take a fresh installed windows 2012 R2 server and its already added to the domain. (Here i do non going to explain how to add information technology to domain as in previous in my posts i explain how to add server to a domain)
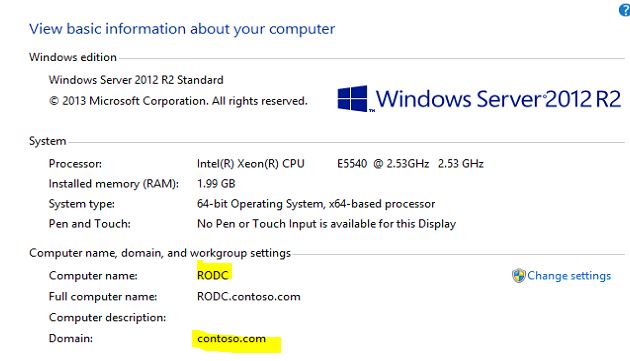
- To begin the setup showtime make sure you login every bit a domain administrator to the server.
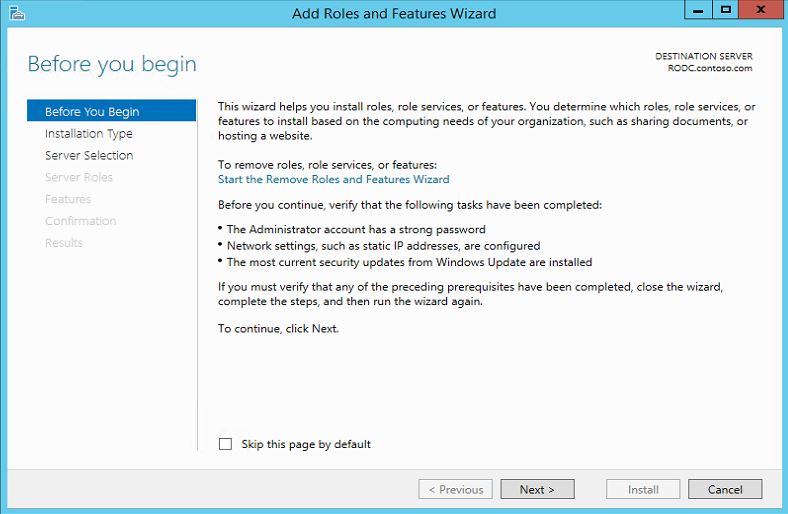
- Open "Server Manager" and from dashboard window click on "Add roles and features"
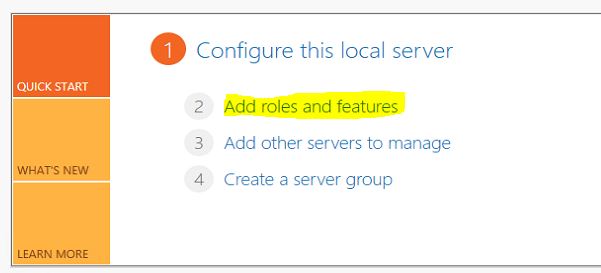
- It will open upward the wizard and click on "side by side" to go on.
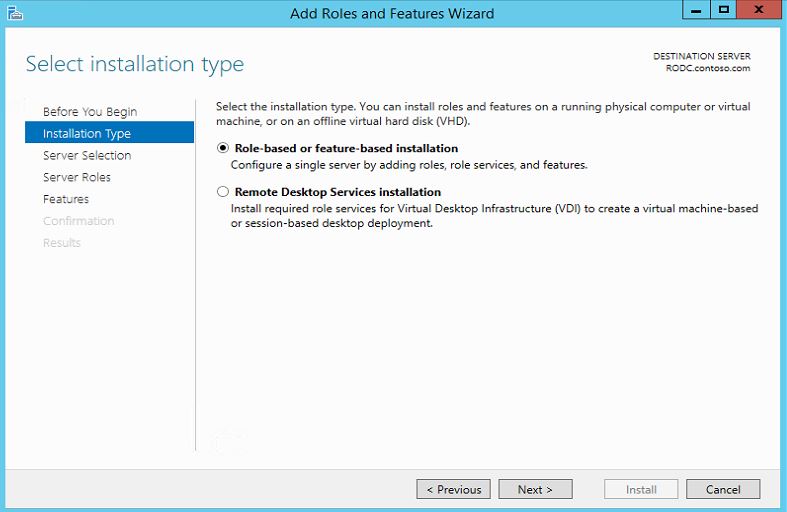
- In side by side window select "Role-based or characteristic-based installation" and click next
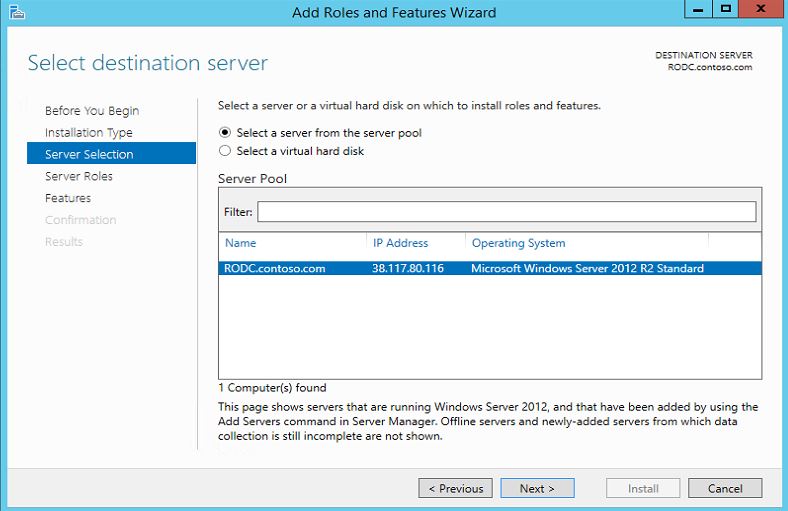
- In next window by default information technology select the current server and click side by side to continue
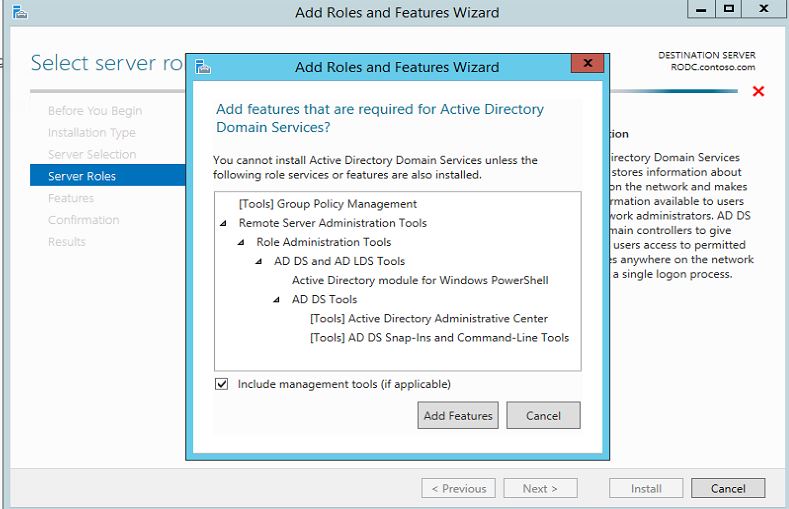
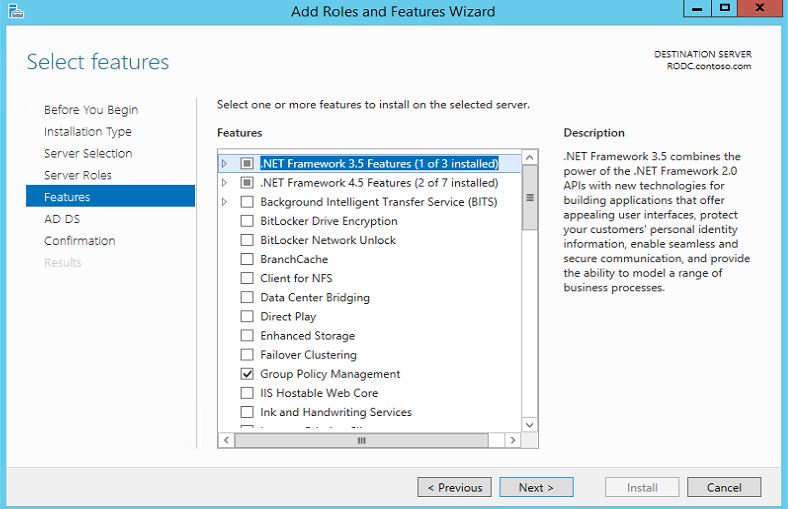
- In next window click on "Active Directory Domain Service" and information technology will pop up with the features. click on "add features" to continue and so "next"
- In adjacent window will allow it run with default features. click on side by side to continue
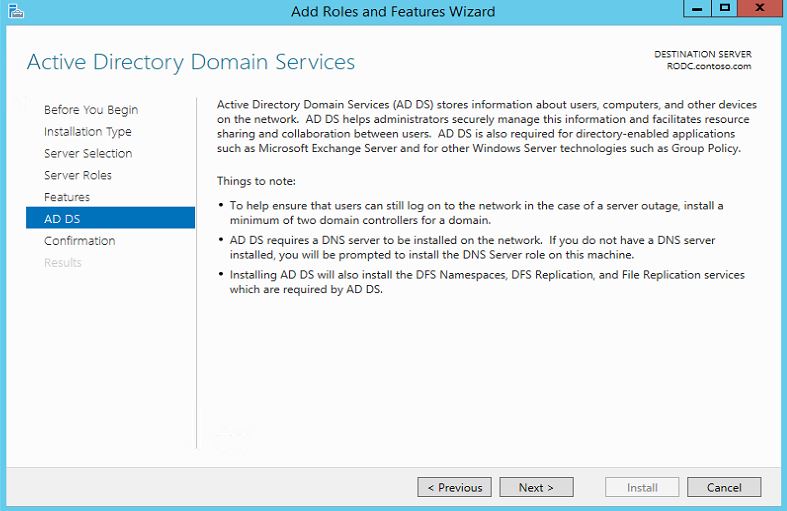
- In next window it will gives brief clarification about the Advertising DS and click next to continue
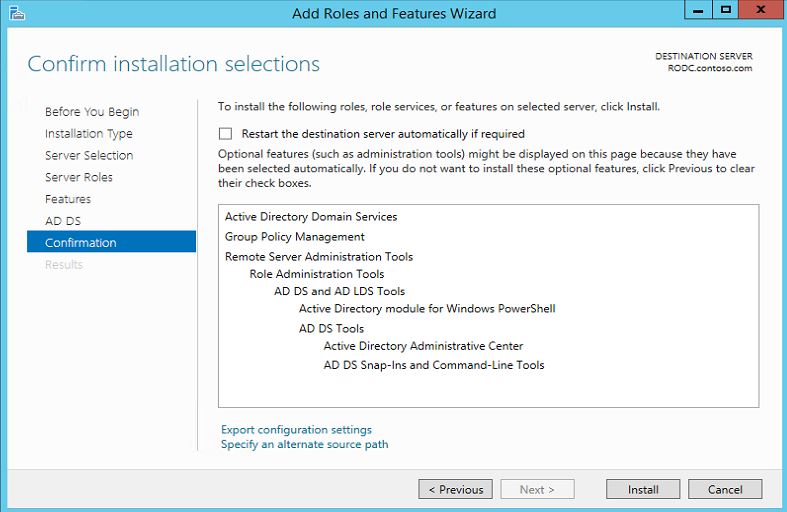
- Next window it volition enquire for confirmation and click ok "install" to begin the service installation
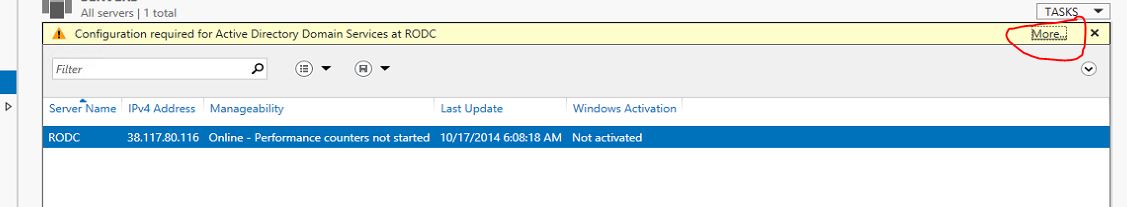
- In one case installation washed open "Server Director" and click on "AD DS"
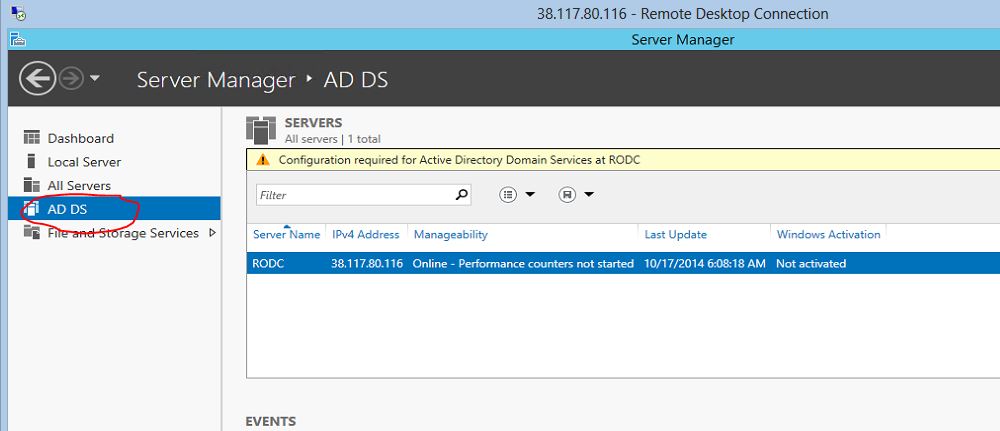
- Then in right paw side panel click "More" every bit in epitome
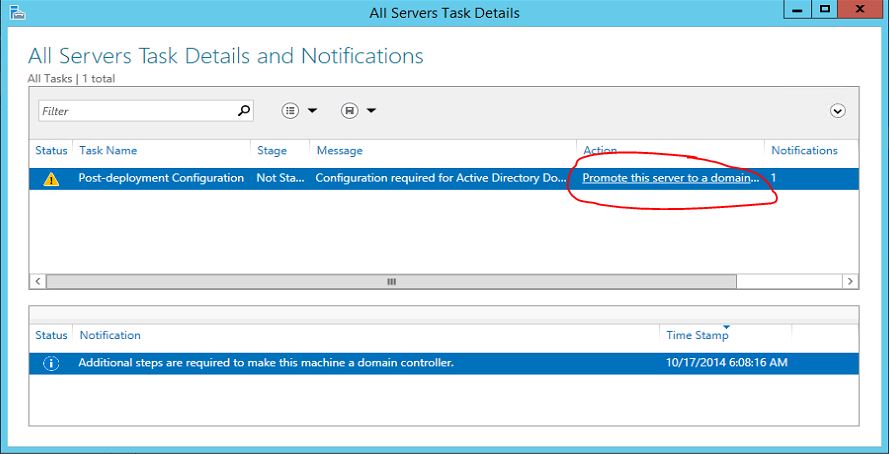
- And so information technology will open upward the wizard and click on option "Promote this server to a domain…"
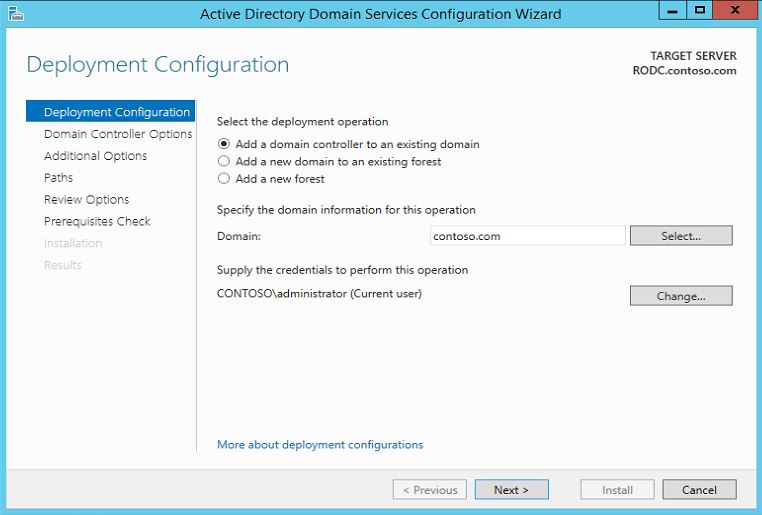
- It will open upwards the configuration wizard. in here we will keep the default selection and click on next to go along
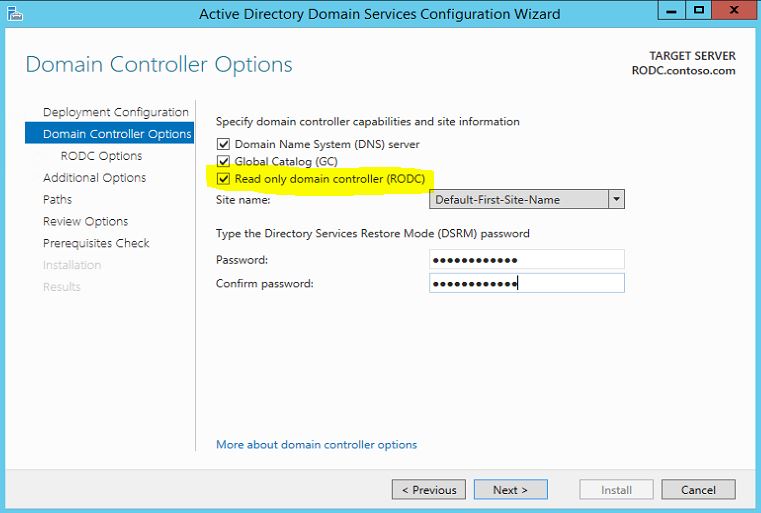
- In next window make sure to select option "Read but domain controller(RODC)" and then also type a password for restore. click on side by side to go on
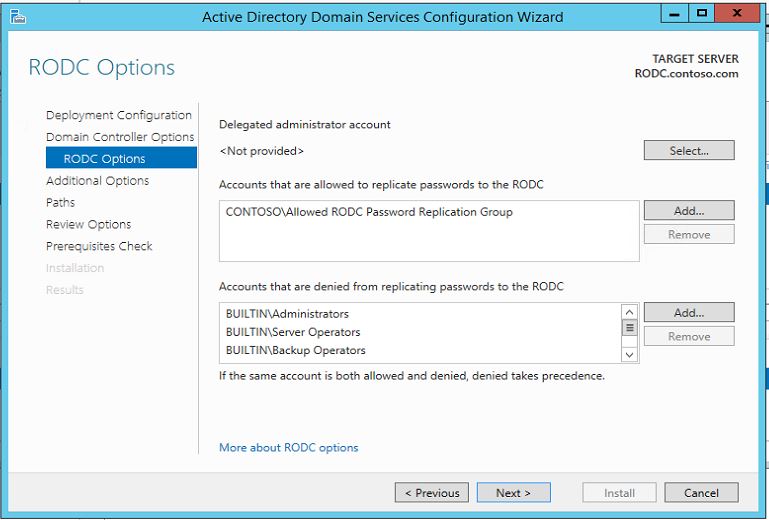
- In side by side window we tin select what groups/users allowed for the password caching, what grouping/users denied for caching and besides delegated admin accounts. in here for now nosotros will keep the default option.
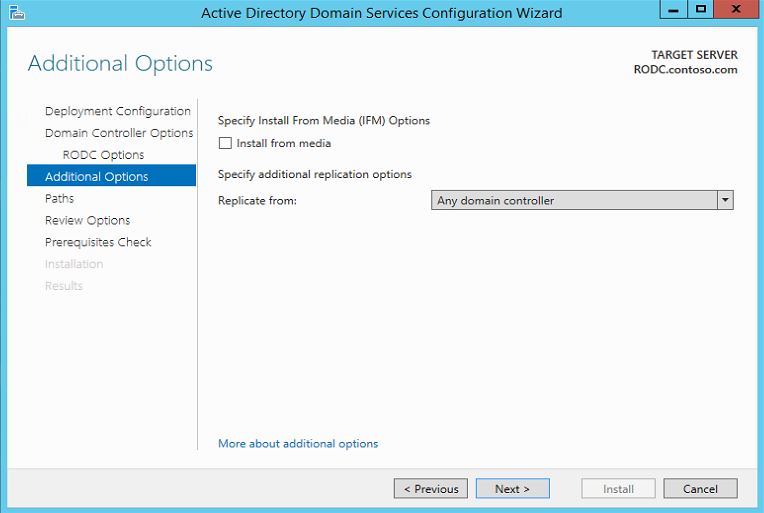
- in next window nosotros can define from which DC nosotros need replication done.
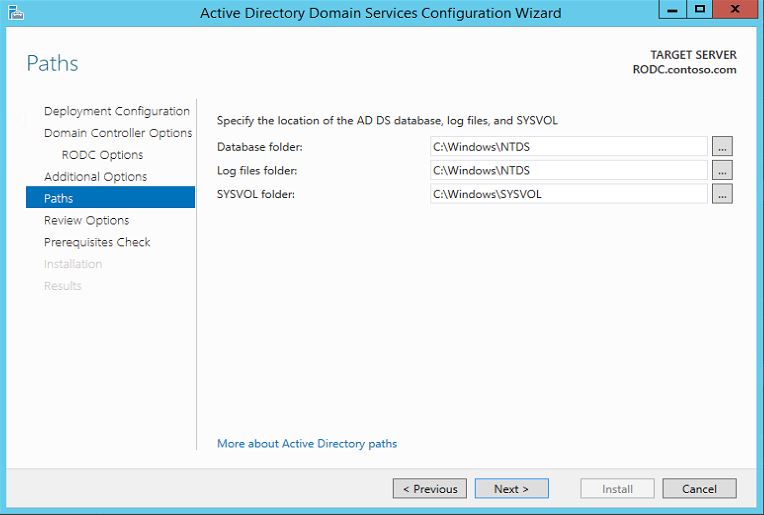
- In side by side window it gives choice to modify the folder paths. in here nosotros keep default. click next to continue.
- In next window it gives option to review the installation selection and click next to keep.
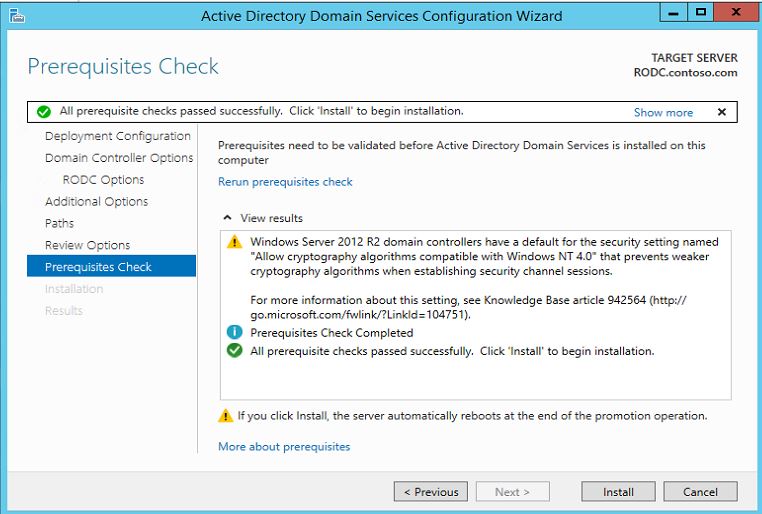
- In adjacent window organisation will check if its meet all the prerequisites for the installation. click on Install to begin the installation
- Once installation done system will automatically reboot.
This completes the installation of RODC in domain. in side by side postal service we volition look in to configuring RODC with different policies.
In enterprise level network its common to have HQ(Head Quarters)-Branch Role network. These branch offices may required to connected with HQ resources for its operations. Most of the time this kind of setup uses WAN links to connect branch Offices with HQ network. Let's presume we have visitor called ABC and its HQ is located in Canada Toronto. Due to the Expansion its need branch office open in London, UK. Then the requirement is more complicated equally its 2 different countries.
The users in London office still demand to authenticate the company domain environment and access the resource. Allow's Look in
to some of the difficulties, challenges faces with typical this kind of setup.
Lack of Resources
To connect HQ with branch site its required secure, reliable connection. But these connections typically comes with high $$$$ cost. Even though its price mostly these links will exist with speed of 128kb, 256kb, 512kb etc. If users in branch site is authenticating company AD it volition apply WAN link for the all the authentication, resources admission etc. if the number of users increase in branch site the link utilization just for the AD activities volition increased. Besides since its betwixt different geographical locations, dissimilar ISP, many facts will affect the reliability of the link as well. what happen if the WAN link went down on critical business day ? so solution is to deploy AD in branch site and it volition be opening whole dissimilar range of concerns, problems.
Security Risks
Even though branch part dc will increase the authentication and resource access process its open potential security risks to the network. some companies will have fully secure datacenter facilities in branch sites as well just majority deceit beget such investments. As we know regular DC is keeping critical information about users, resources authentications etc. what if these branch office dc get compromised or stolen?. It will affect entire company network operations and some fourth dimension this kind of issue tin crusade millions of dollars lost to the company.
Management
If we host a branch site DC, typically it will required maintenance time to time. it may be to deploy fail over dc, upgrade hardware, site-link changes, user credential changes etc. So some time company may need to continue a Information technology department running on branch office which will increment the company functioning price. Also since its integrated direct with main domain surround, whatsoever changes triggers in branch office DC will too directly touch entire domain environs.
So what is the answer then ?
With windows 2008 server Microsoft introduce the Read-Only domain controller feature to specially address these difficulties company face in this kind of co-operative site scenario.
Read-Only!!!!
As its name says its by default Read-but copy of the visitor chief DC. So the changes making on branch site RODC will non affect DC operations. And so basically its keep all the info nigh the DC attributes in Branch-DC every bit read-only copy and once its receive asking for hallmark it directs the asking to the RODC instead going via WAN link.
Password Replication Policy (PRP)
Nosotros tin can also command this "credential caching" in detail level by using Password Replication Policy. what it does is we can define which users, group need the credential caching on that item RODC. For example permit's assume we take some other branch in Bharat. The users in India role will non login from London office anyway. so why we should cache credential info for India function users in London office RODC ? Besides in this style it improve security of dc more than. So if one of branch office RODC compromised it will only hold limited data about the DC.
In windows 2012 server to configure nosotros can utilize two security groups it creates with RODC setup. Co-ordinate to Microsoft its as post-obit,
Immune RODC Password Replication Group : Members of this group are placed in the Permit listing of the Password Replication Policies of all RODCs by default. This group has no members when Windows Server 2012 is first installed.
Denied RODC Password Replication Group: Members of this grouping are placed in the Deny list of the Countersign Replication Policies of all RODCs by default. Some of the groups include Administrators, Server Operators, Backup Operators, Account Operators, and Denied RODC Password Replication Group.
Local Administrators Group
Some time the co-operative offices need some IT support for their users. Information technology may accept local It staff or outsourced IT company for this. In typical DC environment to do the maintenance a detail user demand to accept domain admin rights or delegated permissions. Just in RODC we can define Local administrator accounts which will give full control over the RODC environs and it still will not affect the parent DC setup.
In adjacent mail volition await in to the configuration of a RODC.
Source: https://www.rebeladmin.com/tag/rodc/
Post a Comment for "You need to prepopulate the password for User1 on DC2. What should you do first?"